27,000! That's the number of vulnerabilities discovered in computer systems in 2023. Faced with a 45% increase in cyber-extortion affecting businesses and public administrations, it is urgent for microbusinesses and SMEs (TPE and PME) to strengthen their cybersecurity.
A successful intrusion can have disastrous consequences for production, sales and your company's reputation. It can even harm your customers if private and sensitive data is leaked. To anticipate potential attacks, identify your weaknesses and comply with the GDPR, it is recommended to carry out a cybersecurity audit.
Why is a cybersecurity audit essential for your SME?
A cybersecurity audit allows you to scrutinize your infrastructure, practices, and systems to detect vulnerabilities before they are exploited by cybercriminals.
The graph below, provided by BPI France, illustrates the main methods used by hackers:
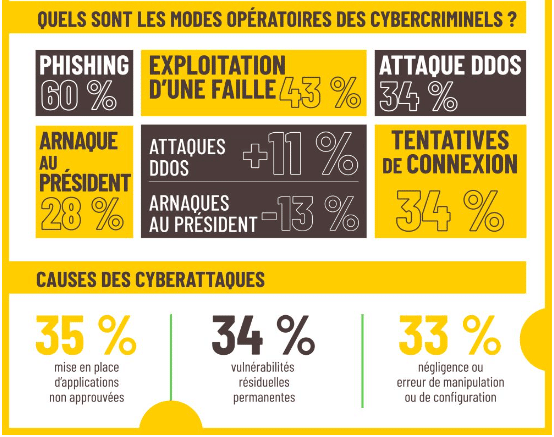
Phishing, accounting for 60% of attacks, remains the most common threat, while 43% of attacks exploit an unpatched vulnerability. These figures clearly demonstrate the importance of a security audit to identify and fix these weaknesses before they are exploited.
In addition, the causes of cyberattacks, such as the use of unapproved applications (35%), residual vulnerabilities (34%) and configuration errors (33%), highlight the need for rigorous security procedures and regular testing.
Moreover, the audit results help you not only anticipate threats but also ensure that you comply with the requirements of the GDPR, thereby avoiding heavy penalties.
The 5 steps to carry out a cybersecurity audit
To be effective, this audit must be carefully organized and structured. By following the five steps below, you ensure you don't overlook any important aspect.
Step 1: Define the objectives and scope of your audit
The first step of a cybersecurity audit is to clearly define your objectives. Are you looking to identify specific vulnerabilities? To verify compliance with the GDPR? Or perhaps to assess the resilience of your infrastructure against a cyberattack?
Once the goal is determined, select the systems, networks and applications that will be analyzed. Also identify systems that need security maintenance regular
For a small business, it's tempting to limit the scope to reduce costs. However, avoid neglecting key elements like remote access, employees' mobile devices and backup systems, which are often prime targets for cyberattacks.
Step 2: Gather the necessary information
Once the scope is defined, the cybersecurity audit begins with a thorough information-gathering phase. This includes reviewing existing documents (security policies, network diagrams), interviewing IT managers, and observing on-site practices.
Our advice:
- Make sure all security policies are up to date and reflect current practices.
- Don’t neglect interviews with employees at all levels. They are often the first line of defense against phishing attacks, and their daily practices can reveal undocumented vulnerabilities.
Step 3: Analyze risks and identify vulnerabilities
According to a CESIN survey, 65% of companies report that cyberattacks have impacted their business, with production disruptions for 24% of them. To avoid these harmful consequences, you must understand where your vulnerabilities lie and prioritize them based on their potential for damage.
To do this, start by mapping all your digital assets: servers, databases, applications, etc. Then evaluate each item to identify potential weaknesses, focusing on the most critical entry points, such as remote access and public interfaces.
Step 4: Test the security of your infrastructure
The testing phase is necessary to identify the flaws that risk analysis might have missed. Two types of tests are particularly useful for micro and small businesses:
1) Vulnerability scan
This automated test detects security flaws in your systems, software and networks. Vulnerability scanning is essential for continuous monitoring, as it allows you to quickly find and fix unintended openings.
For example, after deploying a new server environment, an SMB can use a solution like Nessus, OpenVAS, Intruder, Orca Security or Nuclei to ensure that no misconfiguration or missing update exposes the server to unnecessary risk.
2) Penetration tests (Pentest)
This type of test involves simulating a real attack on your system to identify flaws that hackers could exploit. Tools used often include Metasploit, a powerful platform that allows testing and validating vulnerabilities through exploitation, or Burp Suite for testing web application security.
For example, imagine an online store performs a pentest and discovers that its content management system (CMS) has a critical vulnerability allowing unauthorized access. Thanks to this stage of the security audit, it can quickly fix the flaw and avoid an attack that could have caused the temporary shutdown of its site — a scenario unfortunately experienced by 22% of companies, according to CESIN.
These two types of tests are complementary: while the vulnerability scan provides a quick, continuous overview, penetration tests go deeper to assess the strength of your defenses against specific attack scenarios.
Step 5: Document the results and put an action plan in place
After the security tests, it's time to document the results, for example in a PDF or a Word document, to ensure easy accessibility.
This file must include a detailed analysis of the identified vulnerabilities, an assessment of the associated risks and recommendations to fix them. However, this documentation alone is not enough; it must be translated into a concrete action plan!
This roadmap, which is primarily addressed to the IT team, IT security managers and senior management, should:
- Prioritize fixes according to risk level.
- Detail the measures to be taken.
- Identify the necessary resources.
- Assign responsibilities.
- Establish an implementation schedule.
Finally, each corrective action must be tracked and evaluated to ensure its effectiveness.
Our final tip for conducting a cybersecurity audit
A cybersecurity audit is not a one-off exercise but an ongoing process. After implementing corrective measures, it is important to schedule regular follow-ups to verify the effectiveness of the solutions put in place.
For a micro or small business, cybersecurity can seem complex, but it is essential to a company's long-term survival. To carry out a tailored audit adapted to your needs and budget, call on a cybersecurity consultant on Codeur.com.


